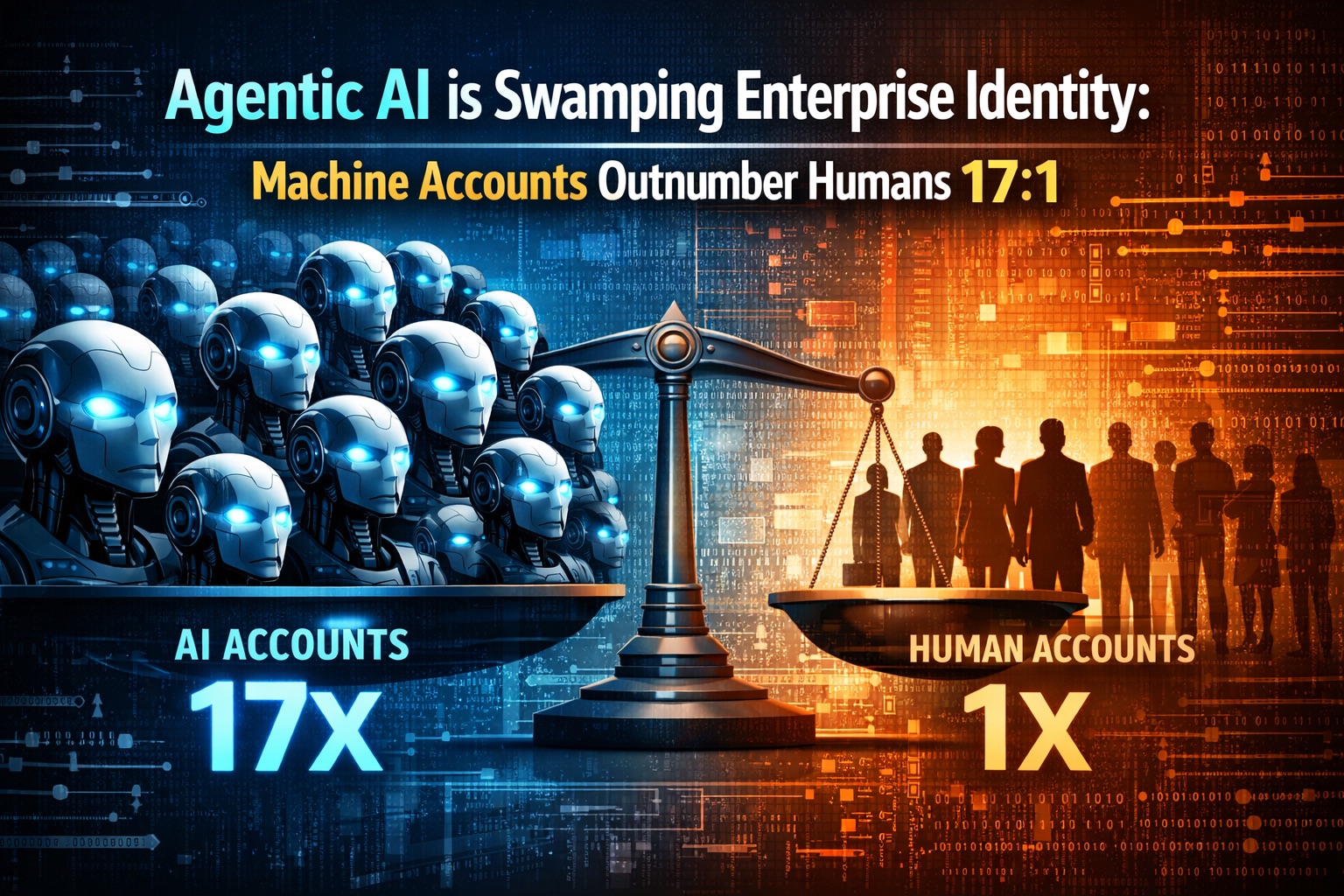
Executive summary: Autonomous workflows are creating a surge of machine identities (service accounts, bots, pipelines), often exceeding human accounts 17:1. This raises audit, security, and compliance risk. Enterprises and public agencies need tighter non-human identity (NHI) governance: short-lived credentials, hardware-backed keys, policy-as-code, and full audit trails.
Why agentic workloads explode identities
Agentic orchestration spins up transient processes, each needing credentials. Ratios of machine-to-human identities now exceed 17:1 in large orgs, driven by cloud, CI/CD, and AI agents.
Controls: JIT creds, short-lived tokens, policy-as-code
Adopt just-in-time access, ephemeral tokens, hardware-backed signing (YubiHSM/TPM), and centralized policy definitions with automated drift detection.
Audit & regulation: SOX/GDPR in the machine era
End-to-end logging of machine actions is mandatory for SOX/GDPR. Map every machine identity to ownership, purpose, and expiry; enforce rotation SLAs.

Yubico – Security Key C NFC – Basic Compatibility – Multi-Factor authentication (MFA) Security Key and passkey, Connect via USB-C or NFC, FIDO Certified
POWERFUL SECURITY KEY: The Security Key C NFC is the essential physical passkey for protecting your digital life…
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Recommendations (Enterprise & Public Sector)
• Inventory: unified NHI catalog with owners and expiry.
• Enforce: mTLS, workload identity, least privilege, and token lifetimes.
• Monitor: anomaly detection on machine behaviors; break-glass paths.
• Certify vendors: require machine-identity hygiene in Gov/enterprise procurement.
Sources: GlobeNewswire, “Non-Human Identity Solutions Global Report 2024-2025 & 2030” (2026-02-05); GlobeNewswire, “Industrial AI…” (2026-02-06)
ephemeral token management software
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
The Agentic A.I. Security Blueprint: 12 Defensive Patterns for Validator Agents and Tool-Use Governance
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
![Free Fling File Transfer Software for Windows [PC Download]](https://m.media-amazon.com/images/I/41Vq6ZqHfjL._SL500_.jpg)
Free Fling File Transfer Software for Windows [PC Download]
Intuitive interface of a conventional FTP client
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.